Gamma PDF Example of how outputs should look: Gamma PDF plot 0.25 0.20 0.15 0.10 0.05 0.00 0 2 6 8 10 Gamma CDF 1.0 Gamma CDF plot 0.8 0.6 0.4 0.2 0.0 0 6 8 10 x Probability density Question - Make a Python Program That Solves the Following Probability Problem (Using Gamma Distribution). Suppose that accidents occur at a particular intersection at a frequency of 16 accidents per year. What is the probability that the third accident will occur before the first month elapses? The random variable in this problem is the time, and in particular that the third accident will occur during the first month. That is, we need to find P(0
Gamma PDF Example of how outputs should look: Gamma PDF plot 0.25 0.20 0.15 0.10 0.05 0.00 0 2 6 8 10 Gamma CDF 1.0 Gamma CDF plot 0.8 0.6 0.4 0.2 0.0 0 6 8 10 x Probability density Question - Make a Python Program That Solves the Following Probability Problem (Using Gamma Distribution). Suppose that accidents occur at a particular intersection at a frequency of 16 accidents per year. What is the probability that the third accident will occur before the first month elapses? The random variable in this problem is the time, and in particular that the third accident will occur during the first month. That is, we need to find P(0
Operations Research : Applications and Algorithms
4th Edition
ISBN:9780534380588
Author:Wayne L. Winston
Publisher:Wayne L. Winston
Chapter12: Review Of Calculus And Probability
Section12.5: Random Variables, Mean, Variance, And Covariance
Problem 5P
Related questions
Question
Make a Python
* If you can answer correctly, I will give you a thumbs up. Thank you!
Transcribed Image Text:Gamma PDF
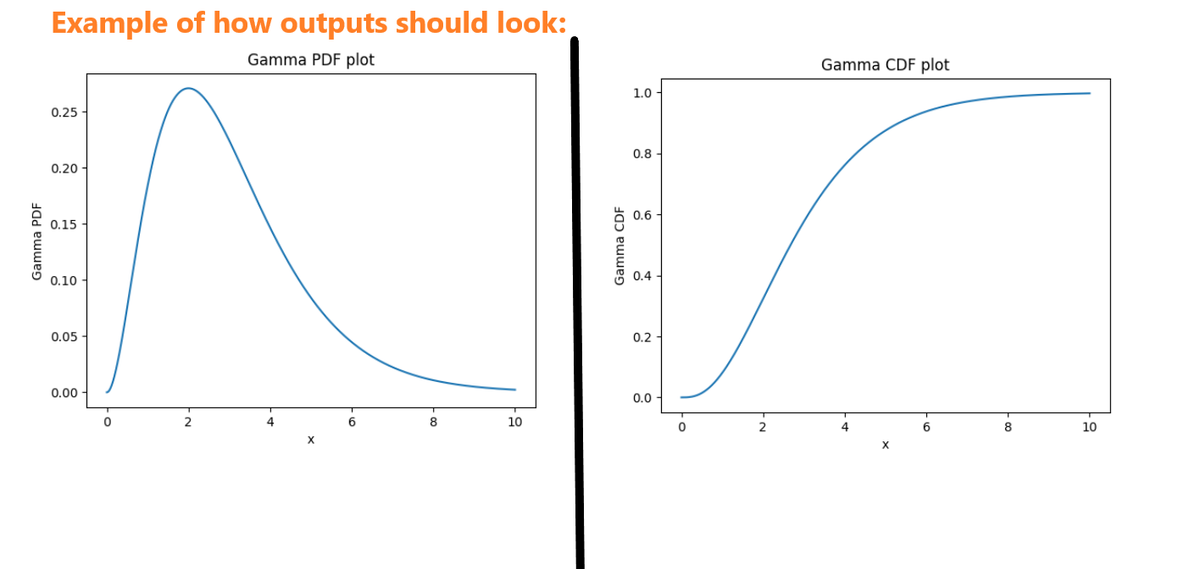
Example of how outputs should look:
Gamma PDF plot
0.25
0.20
0.15
0.10
0.05
0.00
0
2
6
8
10
Gamma CDF
1.0
Gamma CDF plot
0.8
0.6
0.4
0.2
0.0
0
6
8
10
x
Transcribed Image Text:Probability density
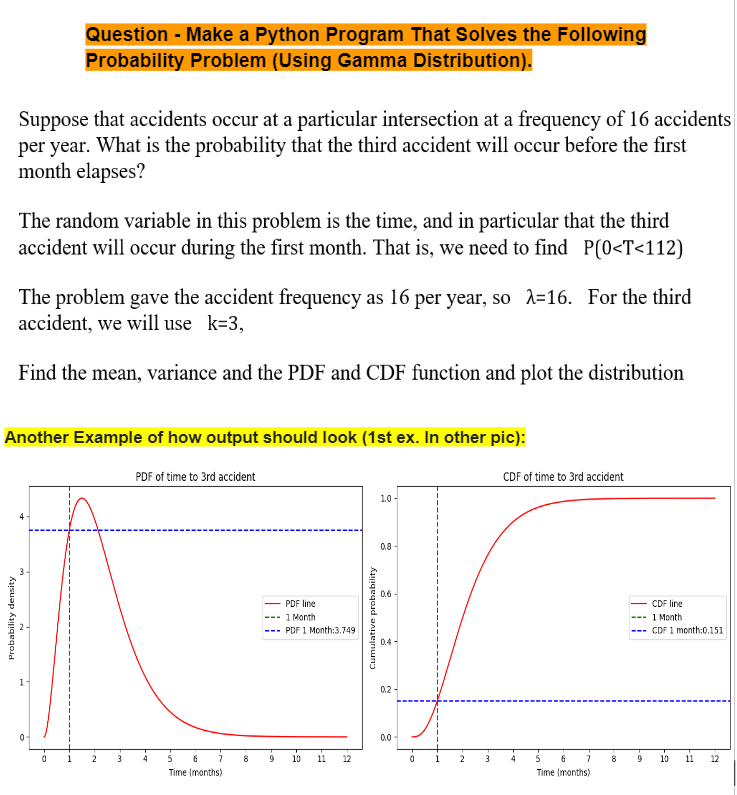
Question - Make a Python Program That Solves the Following
Probability Problem (Using Gamma Distribution).
Suppose that accidents occur at a particular intersection at a frequency of 16 accidents
per year. What is the probability that the third accident will occur before the first
month elapses?
The random variable in this problem is the time, and in particular that the third
accident will occur during the first month. That is, we need to find P(0<T<112)
The problem gave the accident frequency as 16 per year, so λ=16. For the third
accident, we will use k=3,
Find the mean, variance and the PDF and CDF function and plot the distribution
Another Example of how output should look (1st ex. In other pic):
PDF of time to 3rd accident
0
а
2
3
4
5
6
Time (months)
PDF line
-1 Month
PDF 1 Month:3.749
Cumulative probability
0.6
0.4-
0.2-
1.0-
0.8-
CDF of time to 3rd accident
CDF line
- 1 Month
CDF 1 month:0.151
0.0-
00
8
9
10
11 12
0
1
2
3
4
5
6
8
00
9
10
11 12
Time (months)
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

Recommended textbooks for you

Operations Research : Applications and Algorithms
Computer Science
ISBN:
9780534380588
Author:
Wayne L. Winston
Publisher:
Brooks Cole

Operations Research : Applications and Algorithms
Computer Science
ISBN:
9780534380588
Author:
Wayne L. Winston
Publisher:
Brooks Cole