Create an interface MessageEncoder that has a single abstract method encode (plainText), where plainText is the message to be encoded. The method will return the encoded message.
Q: Write an anonymous PL/SQL block that examines the system date and responds to the console window…
A: In the realm of database management, PL/SQL is a powerful tool for Oracle database environments. It…
Q: What do you think the benefits and drawbacks of manual software testing are?
A: What is software: Software refers to a collection of programs, data, and instructions that enable a…
Q: Use only three sentences to sum up each topic: (what/why/advantage(s)/disadvantage(s))Indicators…
A: What is decision: Decision refers to the act or process of selecting a course of action or making a…
Q: The phenomenon of disc thrashing, which refers to the excessive swapping of data between a…
A: Disc thrashing It is also known as "thrashing" This disc thrashing occurs when a computer's…
Q: What is your assessment of the calibre of software updates?
A: Assessing the caliber of software updates is essential in understanding their quality,…
Q: Give a complete breakdown of all the methods that have been used to improve software quality so far.
A: The degree to which a software system or product satisfies predetermined requirements and user…
Q: Create a file called search_replace.py. Here, create a program that implements a search and replace…
A: 1. Create the user-defined function whose name is searchreplace()2. Take the input from the user3.…
Q: Explain the SDLC steps and their outcomes.
A: The Software Development Life Cycle (SDLC) outlines how to create, preserve, and replace explicit…
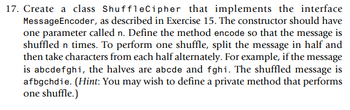
Q: Just how many third-world nations make use of the web and related technologies?
A: Internet penetration implies the percentage of a country's population that uses the net. In many…
Q: When talking about technology, fog means precisely what it says. What does the Internet of Things…
A: The Internet of Things (IoT) refers to the interconnected network of physical devices, vehicles,…
Q: What is the characterization of wireless LAN development?
A: In this question we have to understand what is the characterization of wireless LAN development?…
Q: What sets apart offline social networks from their digital counterparts? Could you elaborate on the…
A: Offline social networks, also known as in-person or face-to-face social networks, refer to social…
Q: Is it possible to differentiate between network services and applications that are cloud-based…
A: In the realm of computing, network services and applications can be categorized based on their…
Q: It's not easy to create, test, and keep up web-based apps in the following industries.
A: Creating,testing,and maintaining web-based apps can be challenging in industries such as…
Q: Explore and identify databases that are relevant to your research or area of interest. What is the…
A: Databases play a crucial role in various fields, including scientific research, healthcare, finance,…
Q: What are the implications of utilising cloud-based applications and services?
A: The utilization of cloud-based applications and services has various implications that organizations…
Q: Explain how a decentralized system could benefit from using generic software components. How would…
A: In a decentralized system, leveraging generic software components can bring several benefits. These…
Q: Explain how a decentralised system could benefit from using generic software components. How would…
A: Decentralized systems are gaining prominence in various domains, such as blockchain networks,…
Q: The present discourse aims to expound on the state of software quality by delving into the domains…
A: Software Quality Assurance (SQA) and Software Reliability are two integral aspects of software…
Q: Explore the performance of the stack in its natural state.
A: What is data Structure: A data structure is a way of organizing and storing data to facilitate…
Q: Is Internet connectivity even available in many undeveloped nations?
A: Internet connectivity in undeveloped nations can vary significantly depending on various factors…
Q: Take a look at the sectors that rely on web engineering and the challenges that they face in…
A: Web engineering plays a crucial role in today's digital age, enabling businesses and organizations…
Q: Examine the utilisation of wireless networks in developing nations. As a result of its benefits,…
A: The utilization of wireless networks in developing nations has seen significant growth and has…
Q: Determine which industries are using web technology, and learn about the challenges associated with…
A: Web technology has become an integral part of various industries, enabling businesses to reach a…
Q: Use a named entity recognition tool to demonstrate the software's functionality. Give an account of…
A: Named Entity Recognition (NER) is a subtask of Information Extraction (IE) that seeks to locate and…
Q: After a software product has been made available to the public, tweaks may be made to it.
A: After the release of a software product to the public, it is common to make adjustments and…
Q: You have a solid grounding in the fundamentals of social media networking. How may cloud computing…
A: What is computing: Computing refers to the use of computers and software to process, manipulate, and…
Q: Contrary to popular belief, the aerospace industry has been successfully building mission-critical…
A: Mission-critical software plays a vital role in the aerospace industry, ensuring the safe and…
Q: What is the physical location of the Left Menus keymap on the keyboard?
A: The physical location of the Left Menus keymap on the keyboard determines where specific keys or…
Q: If individuals have access to the internet, how can that affect their health? What sets telesurgery…
A: In this question we have to understand and discuss on If individuals have access to the internet,…
Q: The two primary types of LAN topologies are mesh and ring. Kindly provide an explanation.
A: The physical or logical configuration of devices in a LAN network is determined by the topologies of…
Q: What are some of the applications of SSH that you have observed? The acronym SSH refers to Secure…
A: Secure Shell (SSH) is frequently abused for management techniques and functions remotely. System…
Q: Software engineering is set apart from other engineering disciplines and fields by certain…
A: Software engineering is indeed set apart from other engineering disciplines and fields by several…
Q: Utilising cloud services offers several advantages in comparison to managing one's own servers and…
A: Cloud services describe the pay-as-you-go internet delivery of computer resources, such as servers,…
Q: Which of the two waterfall methodologies, the conventional or the more flexible iterative approach,…
A: The conventional waterfall methodology follows a sequential, linear approach where each phase of the…
Q: What kind of technological resources (hardware and/or software) does the workflow management system…
A: Workflow management systems (WMS) are essential in organize and scheming the sequence of tasks to…
Q: Write about software testing concepts, issues, and approaches.
A: What is software: Software refers to programs, data, and instructions that enable a computer system…
Q: ut software testing concepts, issues, and approaches.
A: in the following section we will learn about software testing concepts, issues, and approaches.…
Q: The Radio Network Controller (RNC) is accountable for which specific tasks in 3G mobile data…
A: The Radio Network Controller (RNC) is a fundamental component of 3G (Third Generation) mobile data…
Q: a project, it's crucial to decide what kind of documentation the programmer w
A: Documentation is a critical aspect of software development and maintenance. It serves as a guide for…
Q: How well versed are you in the different uses of SSH? Creating a collection of SSH acronyms and…
A: SSH, which stands for Secure Shell, is a network protocol that provides a secure way to access and…
Q: What is the difference between the following two queries? SELECT COUNT(*) FROM products;…
A: What is Database: A database is a structured collection of data that is organized, stored, and…
Q: The concept of computer network reliability and availability pertains to the ability of a network to…
A: Network reliability and ease of use are serious events of a network's recital. Consistency refers to…
Q: In your opinion, what are the top three essential duties of a database administrator? What methods…
A: Database administrators (DBAs) play a crucial role in managing and maintaining databases, which are…
Q: Defining software security and why it matters at every stage of development is essential.
A: Software security refers to the measures and practices implemented to protect software application…
Q: Are there any specific credentials required for software developers working on safety-related…
A: Software developers on safety-connected systems often need specific credentials elsewhere general…
Q: If everything is connected, what role does a real-time operating system (RTOS) play?
A: In the era of ubiquitous connectivity where everything is interconnected, the role of a real-time…
Q: Use a named entity recognition tool to demonstrate the software's functionality. Give an account of…
A: Named Entity Recognition (NER) is a vital characteristic of Natural Language Processing (NLP), where…
Q: Select the option that best represents the advantages and disadvantages of evaluative research.
A: What is Research: A systematic investigation aimed at expanding knowledge, exploring new ideas, and…
Q: The acronym SSH refers to Secure Shell, which is a cryptographic network protocol used for secure…
A: What are some of the applications of SSH that you have observed? The acronym SSH refers to Secure…

Step by step
Solved in 5 steps with 2 images

- Create an interface MessageEncoder that has a single abstract method encode(plainText), where plainText is the message to be encoded. The method will return the encoded message.5. Create an interface MessageDecoder that has a single abstract method decode (cipherText), where cipher Text is the message to be decoded. The method will return the decoded message. Modify the classes 8.5 Graphics Supplement SubstitutionCipher and ShuffleCipher, as described in Exercises 16 and 17, so that they implement Message Decoder as well as the interface MessageEncoder that Exercise 15 describes. Finally, write a program that allows a user to encode and decode messages entered on the keyboard. 703Does it make sense to implement each and every method of an interface while doing so?
- Use java programming language 1.1 Create a Student Object project. Create a Student class and use the provided UML diagram to code the instance fields, constructors and methods. Note: The module mark is the average of the participation mark and the examination mark - calculate this using the calcModuleMark() method. The determineStNumber() method should compile a student number with the first 3 letters of the student's name, a '#' symbol, and a 3-digit randomly generated number (make use of a for-loop to concatenate these 3-digits). The stNumber data field should be set in the constructor by calling the determineStNumber() method. The toString() method must compile a string to display the student number, participation mark, examination mark, and module mark, formatted in table format. Student number PMark EMark MMark Mar#9186 81 64 72.00 1.2 Create a testStudents class. Do the following: -Write a static method called display() which receives…Declare an interface IA with two method Me() and You() in JAVA . Define two classes CA and CB which implement IA such that Me in CA displays it is me in CA and You in CA displays how are you from CA. The same message should be displayed from CB. Use the reference variable of the IA to implement runtime polymorphism.Your assignment for this course is to implement a beginner level Book Management System (BMS) in Java language. BMS contains 2 classes: Bookand BookList. The Book class has the following attributes: code: a String object, that hold the book’s code. title: a String object, that hold the book’s title. qua: int variable, that hold the number of books with the same code in the library. price: a double variable, that hold the book’s price. The BookList class contains only one data member: ArrayList<Book> t. When running the program display the menu as below:1. Input & add book(s) to the end.2. Display all books.3. Search a book for given code.4. Update the book’s price for given code.5. Find the (first) max price value.6. Sort the list ascendingly by code.7. Remove the book having given code.8. Load data from file.0. Exit.Notes:(1) The book’s code must be unique in the list.(2) Display all books in format (code, title, quantity, price).(5)…
- Create an interface MessageDecoder that has a single abstract method decode(cipherText), where cipherText is the message to be decoded.The method will returnthe decoded message. Create a class SubstitutionCipher that implements the interface MessageDecoder as described above. The constructorshould have one parameter called shift. Define the method decode so that each letter is shifted by the value in the shif. For example, if shift is 3, a will be replaced by d, b will be replaced bt e, c will be replaced by f, and so on. Hint: You may wish to define a private methodthat shifts a single character. Create a class ShuffleCipher that implements the interface MessageDecoder. The constructor should haveone parameter called n. Define the method decode so that the message is shuffledn times.To perform one shuffle, split the message in half and then take the charactersfrom each half alternatively. For example, if the messsage is "abcdefghi", the halves are "abcde" and "fghi". The shuffled…How do you define an interface and how do you use it in Java. what happens if anabstract class implements an interface? Is it possible to implement an interfacewithout using all the abstract methods in the implemented class? Elaborate youranswer with proper Examples andexplanations……………………………………………………..only in java not in java c++ Create an interface EnhancedShape that extends Shape and also requires a method public double perimeter( ) to be implemented by any class that uses the interface. Create a class file, an interface ehancedshape extends shape, and an interface shape file.
- Write a Program in Java Create an interface EnhancedShape that extends Shape and also requires a method public double perimeter( ) to be implemented by any class that uses the interface. (Note: Interfaces can inherit other interface just like a class by using extends keyword. Create a class file, an interface ehancedshape extends shape, and an interface shape file).Create an interface that shall have 2 methods and one string type attribute, also create an implementation class of the interface that shall define both methods (you can print YOUR favorite quote in each method body).Please help answer this Java multiple choice question. Assume you are a developer working on a class as part of a software package for running artificial neural networks. The network is made of Nodes (objects that implement a Node interface) and Connections (objects that implement a Connection interface). To create a new connection you call the constructor for a concrete class that implements the Connection interface, passing it three parameters: Node origin, Node target, and double weight. The weight is a double that is greater than or equal to 0, and represents how strongly the target node should weigh the input from the origin node. So with a weight of 0.1 the target node will only slightly weight the input from the origin, but with a weight of 725.67 the target node will strongly weight the input. The method throws an IllegalArgumentException. Which of the following are true? A. All of the above are true. B. The code:Connection c = new ConvLayerConnection(origin, target,…

